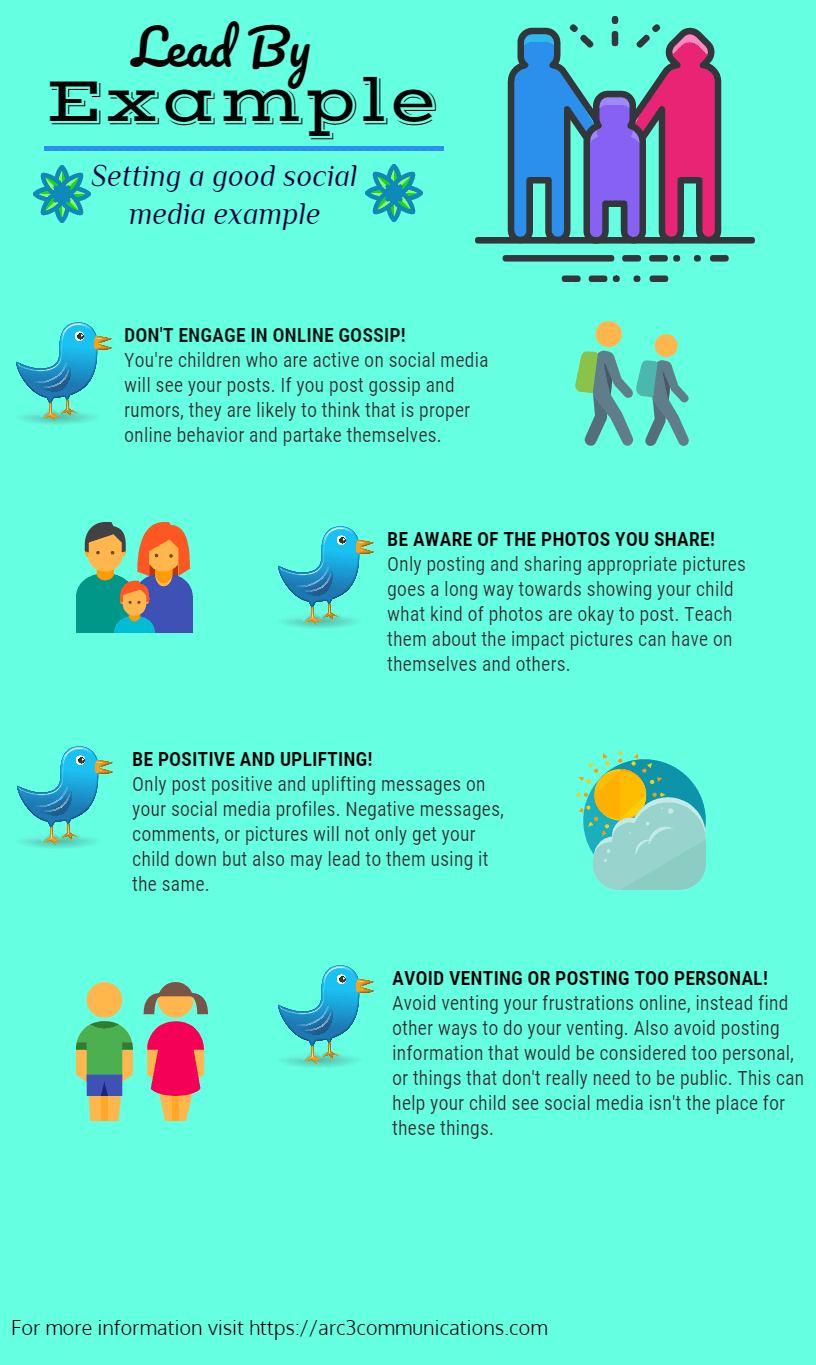
Children model the behavior of their parents and this includes in the digital communities of Instagram, Facebook, Twitter and Snapchat. When parents share posts about their lives, and then monitor these posts for likes and followers, children take note. While parents would never want to post anything that would be a negative influence on their children, there is little guidance to help them navigate parenting in the digital age. Below is a social media parenting guide for how to set a good example for your kids on social media.
Want more info? Check out our in-depth social media tips for parents here and our easy social media parenting guide for discussing social media usage with your kids here.